A new paper by Henry Herrington, a computer science undergraduate at Princeton University, demonstrates that a hacked PDF ballot can display one set of votes to the voter, but different votes after it’s emailed – or uploaded – to election officials doing the counting.
For overseas voters or voters with disabilities, many states provide “Remote Accessible Vote By Mail,” or RAVBM, a system that allows voters the ability to download and print an absentee ballot, fill it out by hand on paper, and physically mail it back. Some states use commercial products, while others have developed their own solutions. In general, this form of RAVBM can be made adequately secure, mainly because the voters make their own marks on the paper.
In some forms of RAVBM, the voter can fill out the ballot using an app on their computer before printing and mailing it. This is less secure: if malware on the voter’s computer has “hacked” the voting app, what’s printed out may differ from what the voter indicated on the screen, and voters are not very good at reviewing the printouts and noticing such changes.
The most dangerous form of RAVBM is one that allows electronic ballot return, in which the voter uploads or emails a PDF file. Thirty states allow overseas voters to do electronic ballot return, either by email, fax, or web-portal upload, as shown in Table 5 (pages 34-35) of Herrington’s longer paper, Ballot Acrobatics: Altering Electronic Ballots using Internal PDF Scripting.
The danger is that malware on the voter’s computer could send a different PDF file than the one that the voter has viewed and verified. A hacker who wanted to steal an election could propagate such malware to thousands of voters’ computers. The malware could alter the operation of the voting app, the PDF viewer, the browser, or the email/upload software. There is a clear scientific consensus on this: According to “Securing the Vote, Protecting American Democracy,” a 2018 report released by the National Academies of Sciences, Engineering, and Medicine: the internet “should not be used for the return of marked ballots . . . as no known technology guarantees the secrecy, security, and verifiability of a marked ballot transmitted over the Internet.”
Electronic ballot return is promoted by technology vendors, Democracy Live and Voatz; and by Nevada, with its own EASE, system, which gives voters “the option of saving the ballot materials as a PDF file and emailing the document as an attachment to the respective county clerk or registrar’s office.” Democracy Live uses OmniBallot, an electronic method of delivering and returning ballots.
In all of these cases, the “final” ballot that the voter reviews is a PDF file.* The election-app vendors are implicitly relying on your intuition that “it’s a document” and we humans think we can read a document. At 8:32 in this Democracy Live promotional video, “this ballot happens to be a document.” Clearly, in the video, it’s a PDF, viewed in a PDF viewer, and from Specter and Halderman (2021) we know it’s a PDF.
It’s dangerous enough that the PDF you view may not be the PDF that’s transmitted to the election administrator. But even if it were the same PDF file, what you see now is not necessarily what you get later.
A recent article by Herrington, “Altering Electronic Ballots Using PDF Scripting,” contains a live demonstration (on page 2) of a PDF ballot that changes what votes are marked from one minute to the next. Of course, a real election hacker wouldn’t produce a PDF whose votes change every minute; the voter might notice that. The real threat model is between verification time and vote counting time. Herrington demonstrates a minute-by-minute change for the convenience of his readers.
A voter might mark a ballot using the EASE, Voatz, or Democracy Live app provided by their county election office, then inspect it using a browser or PDF viewer:
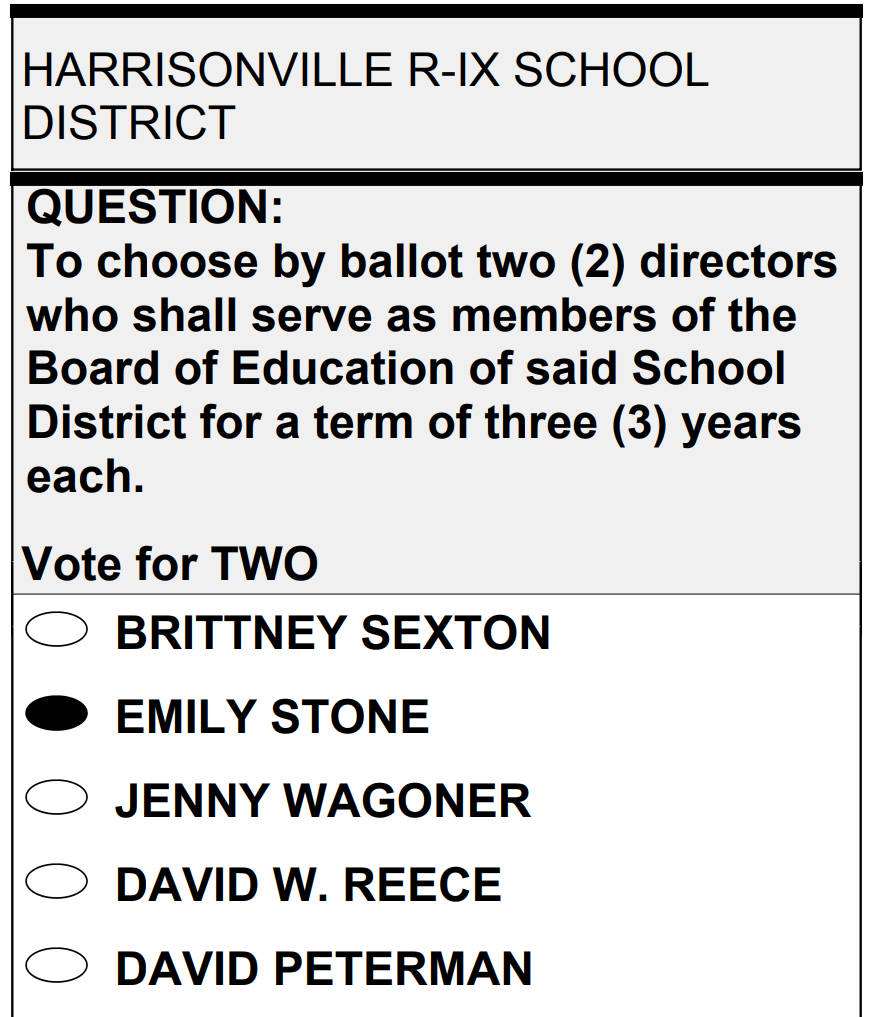
By inspecting the ballot, the voter might think they have verified their selection of candidates. Then they email or upload this PDF ballot, as instructed.
But when the election administrator processes that very same PDF file to count the votes, the filled-in oval has moved from one name to another:
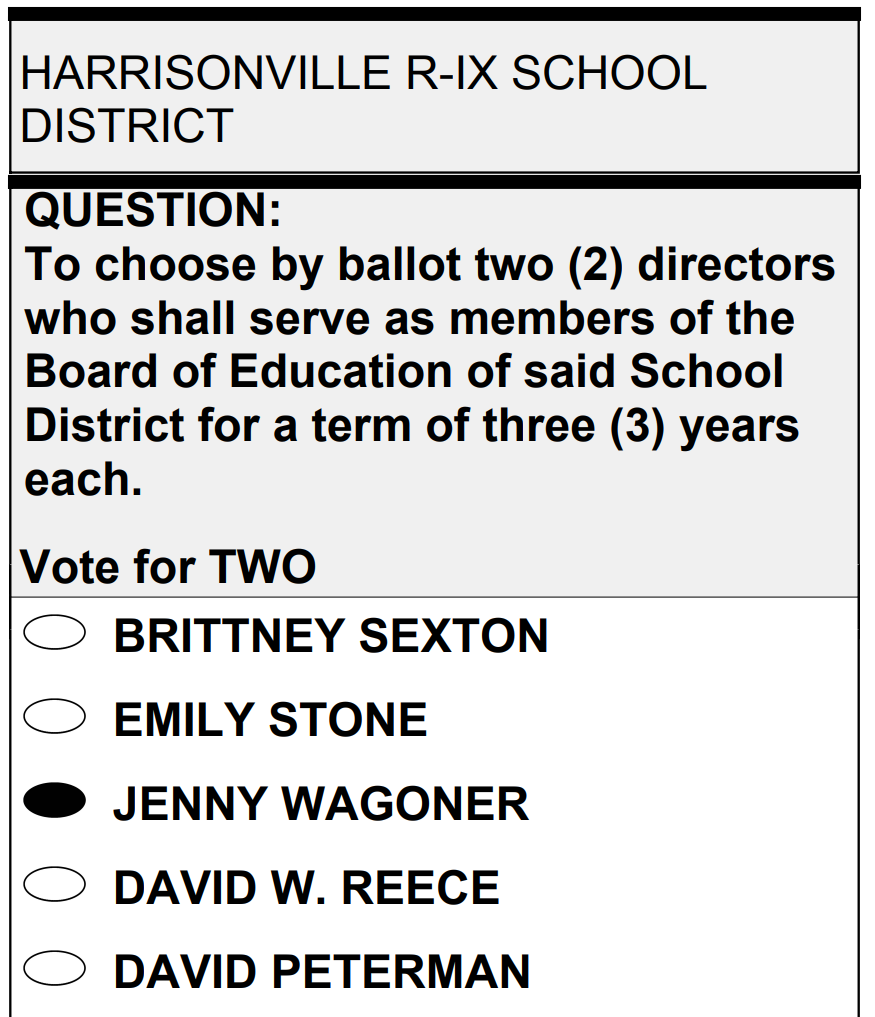
The vote has been hacked!
PDF files are not static; they contain active program software. If a hacker has infected thousands of voters’ home computers with vote-stealing malware, that malware can corrupt the operation of the official ballot-marking app to produce dynamic PDF files.
You might think, “my computer probably isn’t hacked, so I’ll take that risk.” But the real risk is not only your computer. A hacker can spread the same malware to the computers of thousands of your fellow citizens, and steal their votes in that same election—and the election result can be altered. That’s not democracy, that’s hackocracy.
In conclusion: Mark your ballots on physical paper. And tell your state and local election officials not to adopt electronic ballot return. For example, you can refer them to this 2020 report of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), which says, “Electronic ballot return is high risk. Electronic ballot return, the digital delivery of a voted ballot back to the election authority, faces significant security risks to voted ballot integrity, voter privacy, and system availability. There are no compensating controls to manage electronic ballot return risk using current technologies. While many risks associated with electronic ballot return have a physical analog with the risk associated with the mailing of ballots, the comparison can miss that electronic systems provide the opportunity to rapidly affect voting at scale.”
*The use of PDF for this purpose in Democracy Live and Voatz is confirmed by independent peer-reviewed analysis: (1) Specter, Michael, and J. Alex Halderman. “Security analysis of the Democracy Live online voting system.” 30th USENIX Security Symposium (USENIX Security 21), 2021; and (2) Specter, Michael A., James Koppel, and Daniel Weitzner. “The Ballot is Busted Before the Blockchain: A Security Analysis of Voatz, the First Internet Voting Application Used in US Federal Elections.” 29th USENIX Security Symposium (USENIX Security 20), 2020; and, (3) the use of PDF in EASE is stated in plain language on Nevada’s web site.

As a practical point, every voting method has risks, even paper. What many observers may not understand is that election officials are REQUIRED to have an accessible method of remote voting.
I agree that browser-based voting using PDF ballots are vulnerable but the article implies that it is used by Voatz architecture which inaccurate., Voatz is a native iOS or Android mobile app (not browser or PDF based) and votes are recorded on an immutable blockchain for later printing on ballot paper by the election official at the close of voting. This not only reduces error-prone manual handling, it supports transparency by permitting the blockchain votes to be compared with the printed ballots, (which is not possible when ballots are ‘remade’ or ‘adjudicated’ with RAVBM.) Further, some jurisdictions even permit voters to use their Voatz anonymous ID to personally audit their own ballot on the blockchain. These ‘citizen audits’ have been performed many times with no discrepancies.
I believe that any remote voting risk assessment should seek to replace with the weakest remote voting methods first (unencrypted email, fax, unencrypted file upload and PDF based voter-printed RAVBM) and then help refine alternative solutions that meet statutory requirements AND have strong accessibility and security. I agree with the author that all forms of electronic ballot return require objective risk assessment — and for that we need STANDARDS. The Government Blockchain Association (gbaglobal.org) has a working group remote elections and standards and invite researchers to participate.
I have this horrible thought that one might do the same to a tax return.
Then, when it is shown beyond a reasonable doubt that the return was wildly fraudulent (well, one hoped to get away with it) that it must be ‘an error in the PDF’. Plausible deniability…
The hacking of PDF files to corrupt ballots is far from a new idea. I raised concern about it over 20 years ago.