In my examination of New Jersey’s voting machines, I found that there were no tamper-indicating seals that prevented fiddling with the vote-counting software—just a plastic strap seal on the vote cartridge. And I was rather skeptical whether slapping seals on the machine would really secure the ROMs containing the software. I remembered Avi Rubin’s observations from a couple of years earlier, that I described in a previous post.
A bit of googling turned up this interesting 1996 article:
Vulnerability Assessment of Security Seals
Roger G. Johnston, Ph.D. and Anthony R.E. Garcia
Los Alamos National Laboratory… We studied 94 different security seals, both passive and electronic, developed either commercially or by the United States Government. Most of these seals are in wide-spread use, including for critical applications. We learned how to defeat all 94 seals using rapid, inexpensive, low-tech methods.
In my expert report, I cited this scientific article to explain that seals would not be a panacea to solve the problems with the voting machine.
Soon after I delivered this report to the Court, the judge held a hearing in which she asked the defendants (the State of New Jersey) how they intended to secure these voting machines against tampering. A few weeks later, the State explained their new system: more seals.
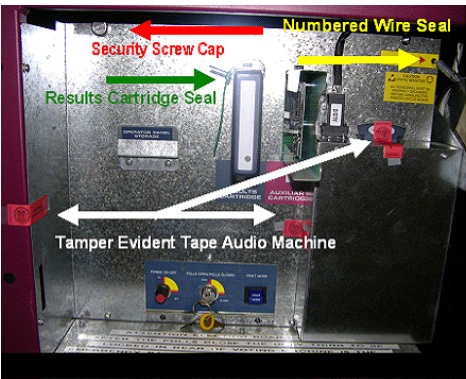
For the November 2008 election, they slapped on three pieces of tape, a wire seal, and a “security screw cap”, in addition to the plastic strap seal that had already been in use. All these seals are in the general categories described by Johnston and Garcia as easy to defeat using “rapid, inexpensive, low-tech methods”.
Up to this point I knew in theory (by reading Avi Rubin and Roger Johnston) that tamper-indicating seals aren’t very secure, but I hadn’t really tried anything myself.
Here’s what is not so obvious: If you want to study how to lift and replace a seal without breaking it, or how to counterfeit a seal, you can’t practice on the actual voting machine (or other device) in the polling place! You need a few dozen samples of the seal, so that you can try different approaches, to see what works and what doesn’t. Then you need to practice these approaches over and over. So step 1 is to get a big bag of seals.
What I’ve discovered, by whipping out a credit card and trying it, is that the seal vendors are happy to sell you 100 seals, or 1000, or however many you need. They cost about 50 cents apiece, or more, depending on the seal. So I bought some seals. In addition, under Court order we got some samples from the State, but that wasn’t really necessary as all those seals are commercially available, as I found by a few minutes of googling.
The next step was to go down to my basement workshop and start experimenting. After about a day of thinking about the seals and trying things out, I cracked them all.
As I wrote in December 2008, all those seals are easily defeated.
- The tamper-indicating tape can be lifted using a heat gun and a razor blade, then replaced with no indication of tampering.
- The security screw cap can be removed using a screwdriver, then the
serial-numbered top can be replaced (undamaged) onto a fresh (unnumbered) base. - The wire seal can be defeated using a #4 wood screw.
- The plastic strap seal can be picked using a jeweler’s screwdriver.
For details and pictures, see “Seal Regime #2” in this paper.

Why don’t they just weld the boxes shut? Too much work?
From time to time they need to remove the circuit-board cover to replace some batteries, or to upgrade the firmware ROMs (with, one hopes, only legitimate upgrades).
I think your reply should have more seriously addressed his proposal. If the machines were designed from the start such that firmware upgrades would need to be done only very rarely, and all of the parts which need to be replaced frequently aren’t secured inside because the design is secure against tampering with them, then welding the access doors shut (preferably with high resolution digital photos of the welds being stored offline) would become a viable, higher security solution.
Nothing will be completely tamper proof. The goal is to make it hard enough that successful tampering is unlikely. Having to get through multiple seals of different types is harder than getting through one seal. It takes more tools and more time, and increases the odds of a mistake that leads to evidence of tampering.
One interesting attack is to not actually tamper with a machine, but make it look like it has been tampered with. The mere appearance of tampering calls into question the reliability of the count, which may be an effective way to the same ends. If the vote is called into question, perhaps your candidate is in a position to be appointed “acting” whatever, or the mandate will be less convincing, or a second election will be scheduled, giving your candidate more time to campaign.
Would things be any better if the seals worked? What are you supposed to do when you come to the end of an election and find all of your machines indicating tampering? You can’t rerun the election.
An even bigger question: what are you supposed to do when you come to the end of an election and find one of your machines indicating tampering?
Don’t forget, some of the attacks can infect the central tabulator with a virus, or spread from machine to machine! Do you hope only the votes in the one machine were b0rked and that their loss won’t significantly skew the election, and just add up the rest? Or do you scrap the whole lot and start over? You can imagine the political/budgetary pressure to do the former and even to cover up the fact of the tamper indications.